ROKU’s Static Analysis Tool and it’s Command Line Utility
ROKU Developers introduced “Static Analysis Tool” which scan’s a channel’s source code for common ROKU development errors. ROKU development team introduces a standalone version of the feature. This simple tool helps developers to regularly analyze their channel during the process of development and identify channel certification violations before submitting a channel for publication.
In this article, we have discussed the static analysis tool and command line utility of ROKU in detail.
Introduction
The channel’s publishing flow includes the “Static Analysis Tool”. ROKU Developers developed this to analyze the channel’s BrightScript source code and detect common issues without having to submit for certification. The ARM developers work with the information they need to optimize their channels and ensure the channel passes certification quickly.
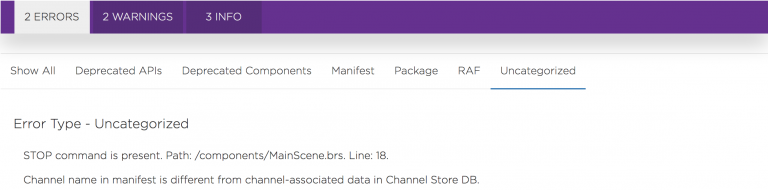
Additionally, the ROKU Developers updated the UI of the Static Analysis Tool’s results within the “Developer Dashboard”. The output is now categorized according to the severity and nature of the issues, making results easier to interpret and act upon. ARM developers can also export the output as a JSON file for their own analysis or record keeping.
So, let us further understand for more clarity on ROKU’s static analysis and command line utility.
What is the Developer Dashboard About?
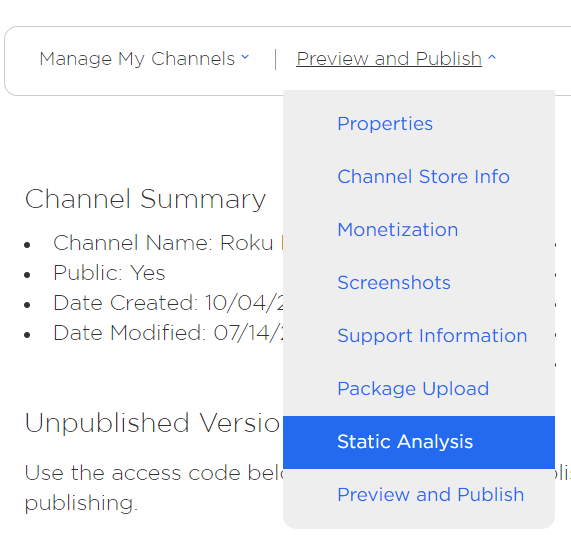
The ARM developer can access the “Static Analysis Tool” from the “Developer Dashboard”.
- To use the Static Analysis Tool, start with uploading a channel package. Refer to “Update an Existing Channel” for the steps “how to upload a package”.
- After uploading the package, the ARM developer will see a “Static Analysis” option in the drop-down box (as shown below).
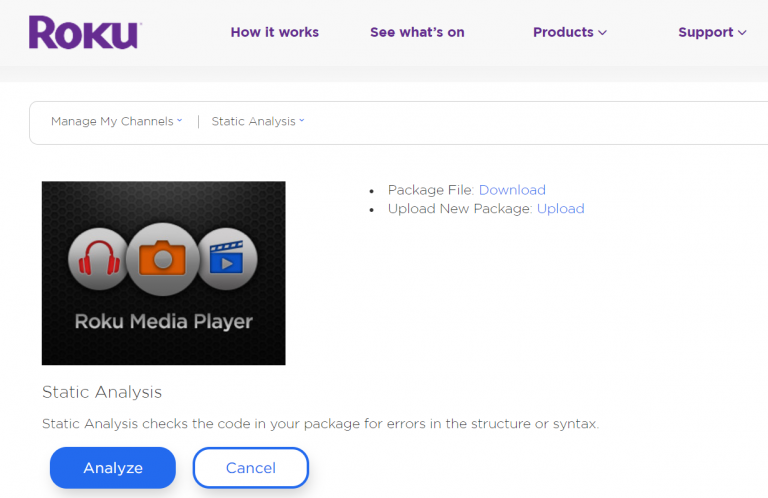
- Below is the Static Analysis dashboard setup. Click on “Analyze” to start the Static Analysis of your channel.
- The following screen indicates that the analysis is underway.
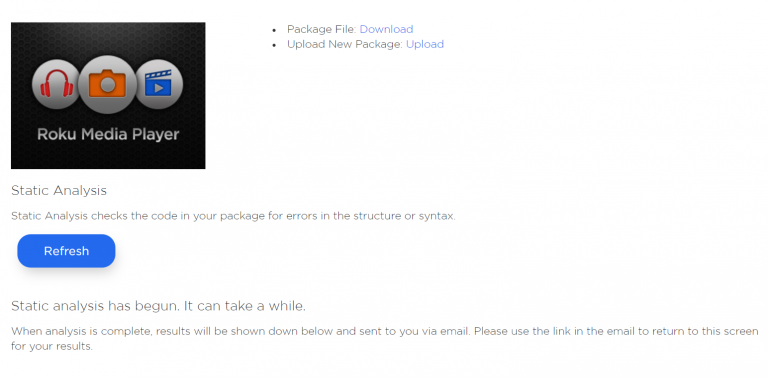
Clicking on the “Refresh” button will check whether the analysis results are ready and if yes, will render them.
- The ROKU developers break analysis results in three categories, broken up by severity. Errors will result in your channel failing certification. Warnings may result in your channel failing certification (now or in the future), or may negatively affect the performance of your channel. The Info section includes information that may be pertinent to your development, but which Roku can not be sure of from a simple Static Analysis scan.
Each of the three major error categories is further broken into sub-categories to better cluster your errors into digestible clusters.
Alternatively, the developer can wait for a notification email sent by the service to the email address associated with their developer account. The sent email will contain a link to the results of the Static Analysis for the channel. The results are available for download as a plain text JSON file as well.
What are ROKU’s Static Analysis Test Details?
The ROKU Development team specifies some tests that Static Analysis performs on the channel package. These may be expanded over time.
- Check for deprecated components
Check for the usage of legacy in UI components. - Check for usage of the TimeGrid (EPG) component
As this component is allowed on a case by case basis, we are checking for its usage in channels. - Check for breakpoints left in code
Check for intentional stopping or pausing place in the code. - Check for potential PII queries
Check for usage of terms like credit, card, age, gender, etc. - Extraneous file inclusion
Channel scanned for files inadvertently packaged with ZIP files (such as the side loadable development app,) __MACOSX artifact folders, .pkg files, etc. - Deprecated manifest entries
Channel scanned for the usage of deprecated manifest flags as specified in the Roku Channel Manifest.
Read Also :-A Complete Guide To Roku’s New IDK
What is ROKU’s Command Line Utility?
This utility performs BrightScript code static analysis. It provides information about common channel issues and checks for compliance with a variety of channel certification requirements, deprecated components and API usage etc.
System Utility
This utility supports Windows, Linux, MAC operating system and Java installation is required.
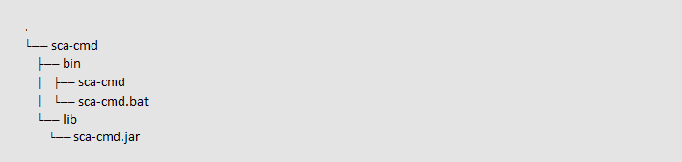
Structure of The Utility
The Static Analysis Utility is distributed as a ZIP file.
Tool Usage from Command Line
Unzip the sca-cmd.zip file to your computer. Note that the usage examples below assume usage on Linux or Mac. There is a corresponding Windows .bat file for Windows users.
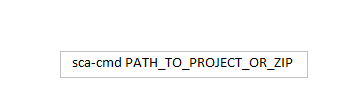
Usage:
Examples:
- sca-cmd myapp
- sca-cmd myapp.zip
Severity level choice
You can specify analysis results output verbosity level using –severity command line parameter. This parameter is optional. The shorthand version -s can be used instead of –severity.
Usage:
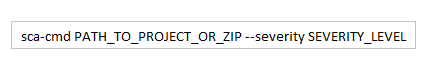
Example:
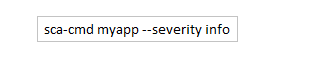
Available SEVERITY_LEVEL values are: info, warning and error :
- info – print all of the logs
- warning – print warnings and errors
- error – print errors only
If the severity level is not specified, warning is used.
Category filter
You can filter output logs by categories using –filter-categories command line parameter. Short version is -c. This parameter is optional.
Usage:
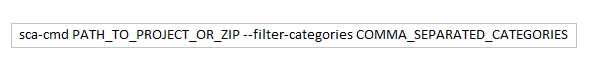
Example:
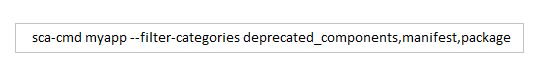
List of categories:
- uncategorized
- deprecated_components
- deprecated_apis
- manifest
- raf
- red
- package
If categories are not specified output logs are not filtered.
Output format choice
You can generate a local report file by specifying the file path in –output and file format in –format command line parameters. Destination folder for report file should be a directory that already exists in your file system. It is possible to use short versions -o and -f instead of –output and –format accordingly.
Usage:
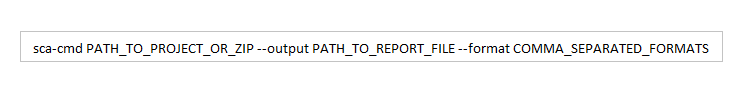
Example:
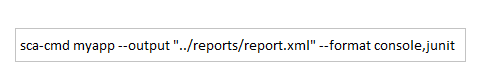
Supported format values are: console and junit:
- console – print all outputs to console
- junit – save all outputs to specified JUnit xml file
If the format is not specified console is used. If specified any file format but not specified output file path a default file path value is used. For junit, this is reports/SCA_Report.xml. For json, this is reports/SCA_Report.json.
Read Also :-https://4waytechnologies.com/blog/how-to-develop-and-publish-vizio-app-for-smart-tv/
Conclusion
We hope you will find this article helpful as it will help you in understanding some impeccable facts about ROKU’s static analysis tool and it’s command line utility in an outstanding way. For more information or software solutions related to ROKU, contact 4 Way Technologies to get the most robust and feature-rich IT solutions.

A freelancing blogs and e-books writer who keeps you up with the trending technologies and user guides. A blogger who is currently a post-graduate living in United Kingdom and trying to make her niche as a Data Scientist. Before taking a deep dive into the "Data-World", she got a Bachelor's Technology degree in Computer Science and has always dreamed of writing as a kid which inspired her to write wonderful content with the right amount of technical terms to make it easy for the beginners and as well full-fledged developers to grasp a hold onto the computer technologies.